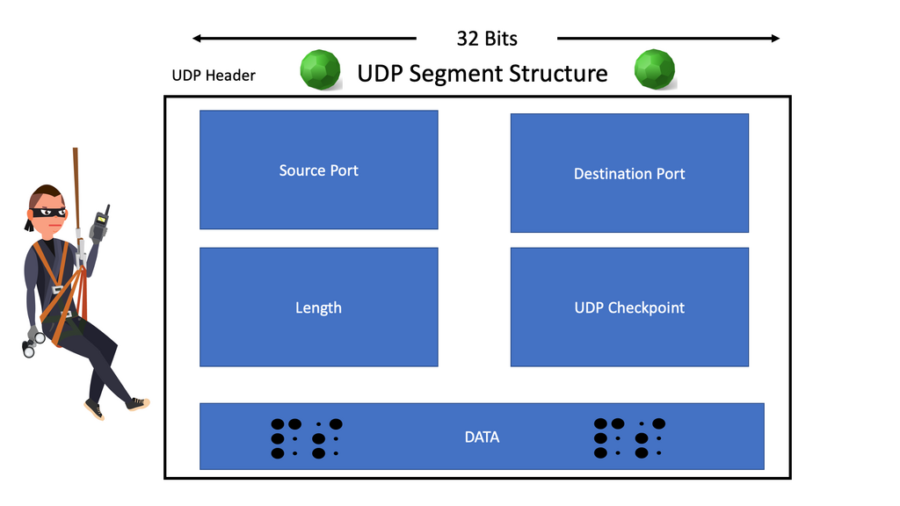
Detecting UDP-based Amplification Attacks_Security Technologies and Applications_Best Practices_UDP-based Amplification Attack Check_Huawei Cloud

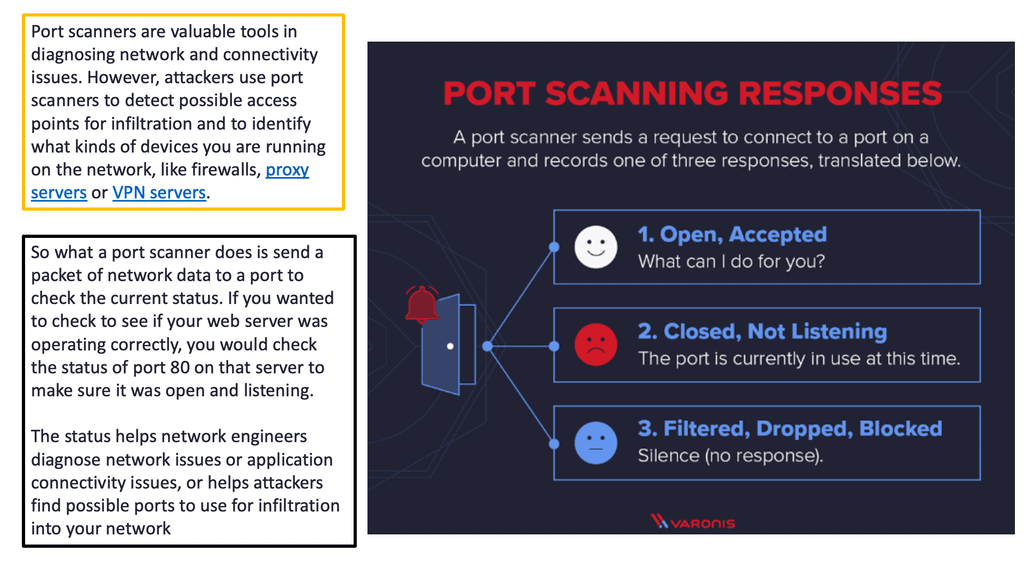
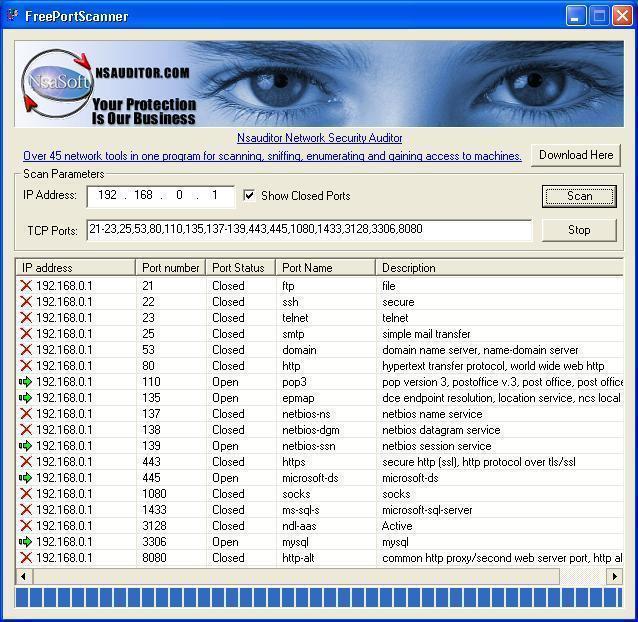
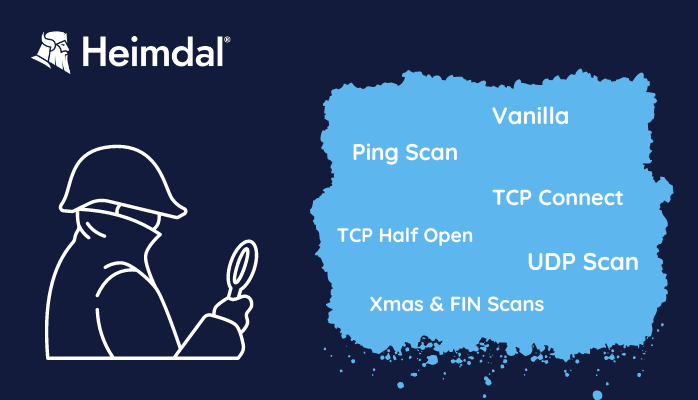
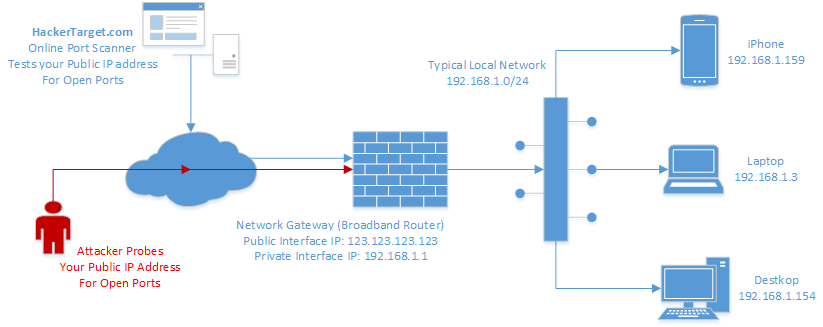
External Attacks: Port Scan_Security Technologies and Applications_Best Practices_Host Security Checks_Hosts Security Issues_Huawei Cloud
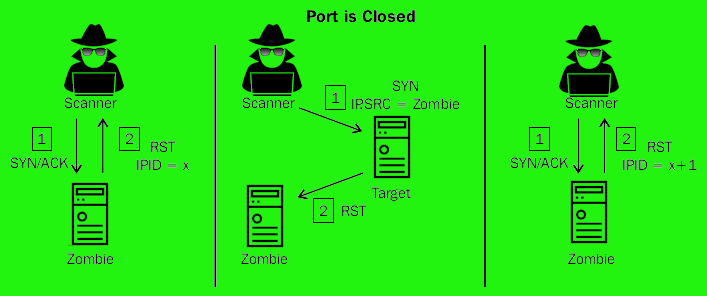
![PDF] Alternative Engine to Detect and Block Port Scan Attacks using Virtual Network Environments | Semantic Scholar PDF] Alternative Engine to Detect and Block Port Scan Attacks using Virtual Network Environments | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/1b227ea0f684755183d7c36873c00a853f2e9f73/3-Figure1-1.png)